February 16, 2021
Single sign-on (SSO) is an authentication method through which users can log in to multiple services by being authenticated only in one of the services. This free business from the need to hold passwords in their databases, login troubleshooting, and decreases the damage a hack can cause.

One of the most common examples of SSO is Google apps. By signing in to the Google accounts, you can access any services of Google, like Gmail, Drive, Slides, Docs, etc.
Benefits of SSO
- Users only need to remember one set of login details. By being authenticated, at your website, you can log in to other services and applications. It lessens the pain of registering for new services or applications. As it is hard to remember the login credentials of each of the applications or services.
- With SSO, the user experience is improved as it avoids lengthy sign-up and authorization processes.
- SSO provides higher security as there is only one point where we need to focus on security. Instead of worrying about the security of many applications.
- With SAML, you don’t have to maintain account information across multiple services. The identity provider bears this burden.
Technologies for SSO
Many technologies are used to provide a Single Sign-On feature. The two most commonly used techniques for providing SSO functionality are OAuth and SAML. Both of these technologies authenticate a user and provide him access to other services and applications. But the working of Both the technology is different.

When we talk about Single Sign-On (SSO), many technologies come to our mind. A few are listed below:
- Federated Identity Management (FIM)
- OAuth (specifically OAuth 2.0 nowadays)
- OpenID Connect (OIDC)
- Security Access Markup Language (SAML)
- Same Sign On (SSO)
In this blog, we will be learning about the SAML workflow. As each of the above terms is a big topic in itself.
Security Access Markup Language (SAML)
SAML stands for Security Assertion Markup Language. It is an XML-based open-standard that allows identity providers (IdP) to pass authorization credentials to service providers (SP). It means that you can use one set of credentials to log in to many different services or applications. SAML use Extensible Markup Language (XML) for standardized communications between the identity provider and service providers.
Now, you must be thinking about what IdP and SP are. So, SAML has two types of providers — Identity Provider and Service Provider. Let’s learn more about these two.
Identity Provider — An identity provider is an application that performs authentication and verifies the user using the login credentials. The identity provider sends a SAML Assertion that is an XML document to the service provider that contains the user authorization.
Service Provider — After successful authentication from IdP, the user redirects to the service or application he or she wants access to. This service or application is known as Service Provider (SP).
SAML Workflow
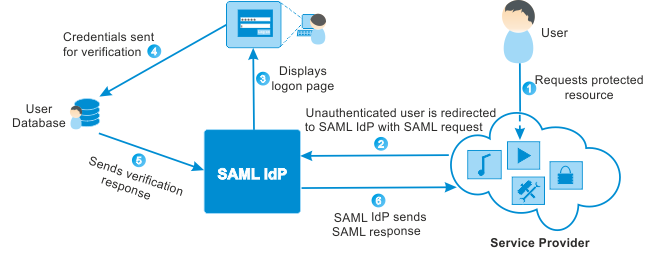
A SAML IdP generates a SAML response in an XML document based on the configuration that is mutually agreed to by the IdP and the SP. After receiving the SAML assertion, the SP validates the assertion by checking if it is coming from a valid IdP and then fetch the required information from the assertion: the username, attributes, and so on.
To do the above process, the SP requires the following:
- Certificate — SAML signing certificates ensure that messages are coming from the expected identity and service providers. The certificate is stored on the SP side and used whenever a SAML response arrives.
- ACS (Assertion Consumer Service) Endpoint URL — This is the endpoint provided by the SP where SAML responses are posted. The SP needs to provide this information to the IdP.
- IdP Sign-in URL — This is the endpoint on the IdP side where SAML requests are posted. The SP needs to obtain this information from the IdP